Comarch Cyber Security software
 Comarch Cyber SecurityComarch Cyber Security products
Comarch Cyber SecurityComarch Cyber Security products
Your assets kept safe from unauthorized access Comarch Smooth AuthenticationWhere online fraud ends and smooth user experience begins
Comarch Smooth AuthenticationWhere online fraud ends and smooth user experience begins
Comarch Cyber Security
Information security products
Comarch has prioritized information security and cyber security software starting from its very first IT project. Ever since the World Wide Web emerged, online data has been exposed to the risk of interception or damage, so ensuring the data is as secure as possible became essential.
There are two elements of IT security we place special emphasis on: strong user authentication and authorization. The former confirms user identity, while the latter grants the user access to a given resource at specific times and for specific reasons.
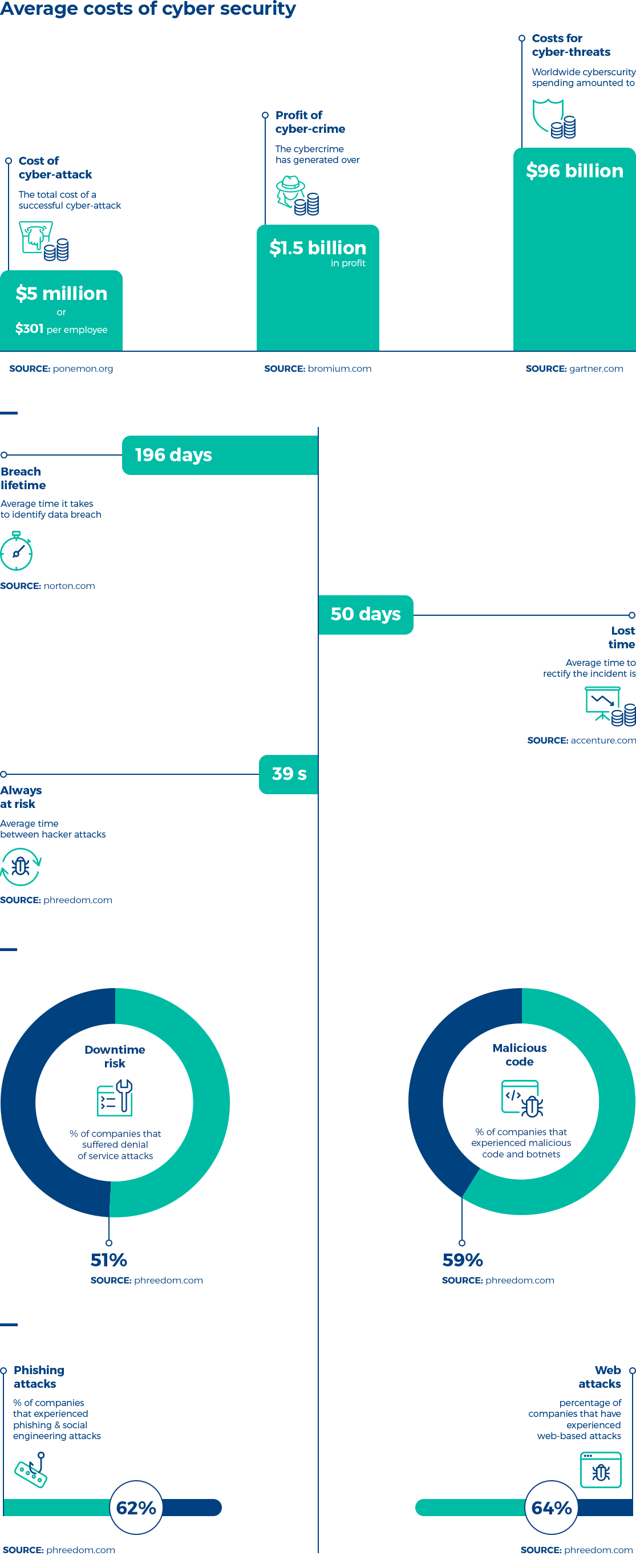
Today, many enterprises are not aware of numerous cyber threats and their security protection level is insufficient. Also, the number of cyber-attacks on various organizations is constantly growing. It’s not only the money these days, but also identities, permissions or access credentials at risk of being stolen or defrauded.
These issues were the main triggers for the preparation our cyber security software products. We work on the cyber security software aspects as early as in the design phase, based on the “security-by-design” paradigm.
Securing Enterprise Authentication Without Sacrificing User Experience
Find out our white paper written in cooperation with Cyber Security Hub and boost your company security with no extra friction.
Download now!Find cyber security software dedicated to your industry
- Comarch tPro – a family of software and hardware cryptographic tokens, designed to protect customer and transaction data by providing secure two-factor authentication and authorization.
- Comarch IAM – an identity and access management software that provides wide control over access to company applications and resources.
- Comarch Smooth Authentication - a monitoring solution designed to guard firms and institutions against online frauds.
We also offer security audits, focusing on risk analysis, penetration tests, standard compliance, guidelines and good practices.
Comarch Cyber Security department has specialized in the research and development of advanced technology solutions for IT security. In the last 20 years, based on our extensive technical knowledge and professional experience, we have completed more than 300 projects for about 50 clients around the world, such as banks, telecoms, or healthcare and government entities. We have also taken active part in the EU projects, where we were always highly evaluated.
Facts about Comarch Cyber Security
Comarch has become one of the largest providers of PKI-based cyber security software for corporate banking in Poland, with clients such as ING, Alior, Pekao, BNP Paribas or DnB Nord.
Comarch’s hardware products are developed entirely within our own technology park, which guarantees full control over each development stage.
Comarch’s products are pioneering in many aspects, and the approach we take is followed by other security solutions (e.g. push-button tokens, driverless tokens).
Since 2018, Comarch has owned the European patent for tPro Touch, one of the most technologically advanced transaction protection software on the market, made for high-risk transactions.
- 1999The first version of Comarch IAM (1.0) known as Protector LS
- 2002Integration with PKI (release 1.1)
- 2007Technical upgrade of authentication engine, support for SAML 2.0 integration (release 1.5)
- 2008 - 2015Support for nearly 400,000 microprocessor cards and tokens compliant with the PKCS#11 standard
- 2009New technology stack and redesign of administration console requirements; the new product version of Comarch IAM (2.0) is called Draco
- 2010Integration with Active Directory, full integration with Comarch Corporate Banking platform (release 2.1)
- 2012Proprietary applet for microprocessor cards matching user biometric data based on match-on-card - one of five in the world (support for UPEK, PreciseBiometrics)
- 2013Proprietary card reader with integrated UPEK fingerprint reader
- 2014Tempest microprocessor card reader with integrated matrix fingerprint reader for the military
- 2014CCP software enabling communication between a web browser and PKCS#11-compliant readers – without additional browser extensions
- 2014World's first HPD (Human Presence Detection) token to prevent remote attacks, based on the elliptic curves cryptography – tPro ECC
- 2015World's first push-button token that does not require driver installation (driverless, zero footprint, ETH interface) – tPro ETH
- 2016New administration console design (SPA principle), support for OpenID Connect integration
- 2017New technology stack (Comarch IAM 3.0) and workflow modifications required by GDPR regulations as well as integration with tPro ECC token;
- 2018Patent for tPro Touch device (hardware WYSIWYS)
- 2017 - 2019tPro Mobile/SDK mobile platform dedicated to strong user authentication and transaction authorization
Our achievements
- Support for nearly 400,000 microprocessor cards and tokens compliant with the PKCS#11 standard
- Applet for microprocessor cards matching user biometric data based on match-on-card - one of five in the world (support for UPEK, PreciseBiometrics)
- Proprietary card reader with integrated UPEK fingerprint reader
- CCP software enabling communication between a web browser and PKCS#11-compliant readers – without additional browser extensions
- World's first HPD (Human Presence Detection) token to prevent remote attacks, based on the elliptic curves cryptography – tPro ECC
- World's first push-button token that does not require driver installation (driverless, zero footprint, ETH interface) – tPro ETH
Cyber Security Blog
Our competences have been confirmed by international certificates





It is vital for every company to regularly check the security of its applications to eliminate potential vulnerabilities which enable hackers to easily access, alter and steal sensitive business data.
This is why, for us, building software is one thing, the other one revolves around consultancy projects whose aim is to double-check whether your IT security is solid. Our experts can:
- identify your company’s security gaps and critical vulnerabilities
- determine attack vectors that expose you to probable threats and breaches
- ensure your compliance with industry security standards
On the basis of those audits our consultants prepare and deliver the best possible IT security solution to protect your resources.
Comarch Cyber Security Professional Services are rendered by highly qualified engineers with wide experience in developing and implementing cyber security software policies that comply with international standards (COBIT, ITIL, TOGAF, MODAF, DoDAF, ISO/IEC 27001, PCI DSS, SABSA).
We specialize in application audits, penetration tests, and compliance & in-project security advisory.
Tell us about your business needs. We will find the perfect solution.