Comarch Smooth Authentication
Turn a problem into a solution with Comarch Smooth Authentication
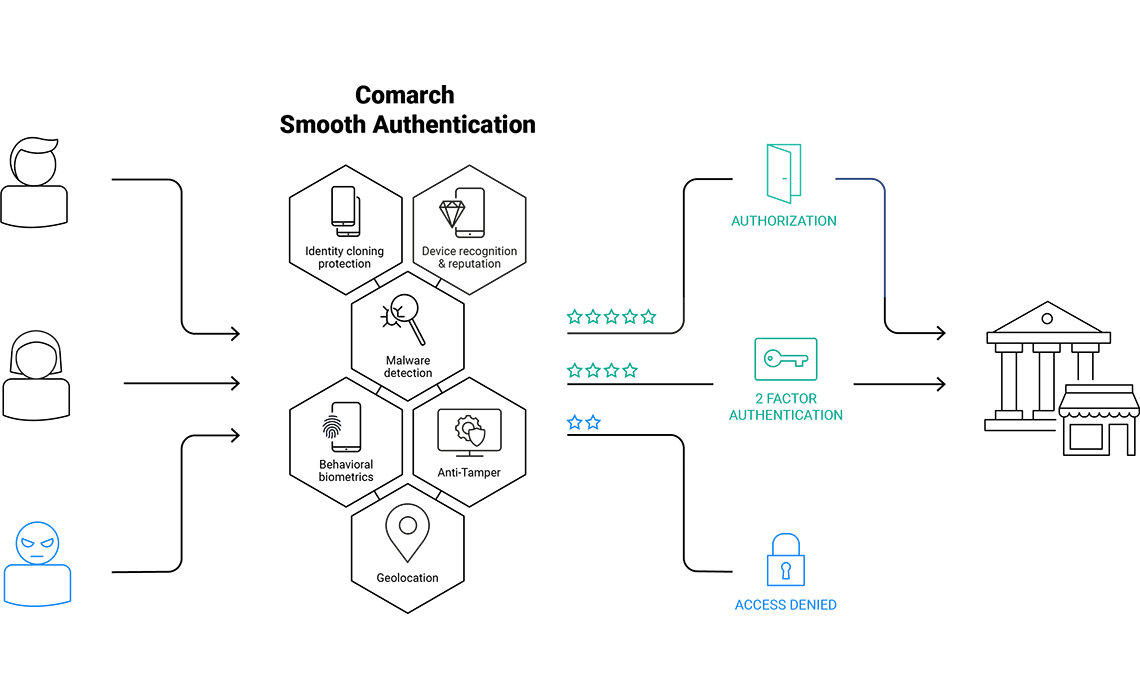
Comarch Smooth Authentication is a risk-based authentication software that combines device recognition, malware detection, and behavioral biometrics capabilities in order to detect frauds in real time. Risk-based authentication allows you to grant your customers with secure and truly frictionless customer journey. It provides exceptional protection from online frauds while building your position as a trustworthy partner.

Detect Account Take Over (ATO) attempts in real time

Distinguish cyber criminals from legitimate users

Provide secure application environment to your customers and keep top-level usability
Invisible layer of extra security without compromising user experience
Customers expect secure operations with your application. But forcing them to constantly verify their actions with PIN codes, one-time passwords, tokens, etc., impacts their experience and causes a significant decrease in conversion rate. Why not make the authentication and authorization process smooth with a risk-based authentication software, operating constantly in the background without involving the end user?
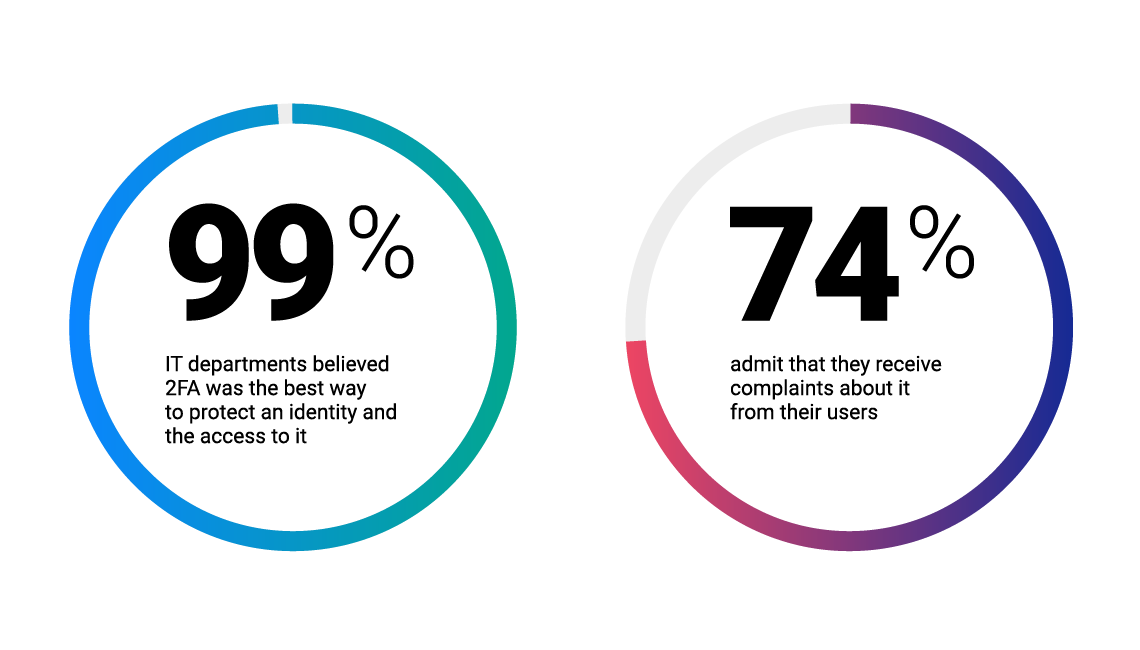
source: Betanews
Comarch Smooth Authentication software analyzes multiple artifacts coming from end user devices, behavior, and software installed on user devices, in order to calculate risk rating for each transaction. This concept of adaptive, risk-based authentication allows to strike balance between security and usability – the second factor is used only when explicitly needed and end customers can enjoy frictionless experiences.
Explore Comarch Smooth Authentication product video

Our risk-based authentication solution allows to verify:
Who can benefit?
Comarch Smooth Authentication software is made for every company that provides their customers or employees with mobile or web access to their services. The risk-based authentication approach lifts fraud protection to the next level in:
- Banking
- Loyalty programs
- E-commerce
- Healthcare
- Corporations
- And more.
What’s in Comarch Smooth Authentication for you?
- An additional security layer with our risk-based authentication and authorization tool, which is a powerful solution analyzing data coming from users in order to protect them against online frauds:

- Protection of both mobile and web channels
- Easy and quick deployment: SDK (for mobile) or javascript (for web channel) embedded into your application
- Business dashboards to monitor fraud statistics
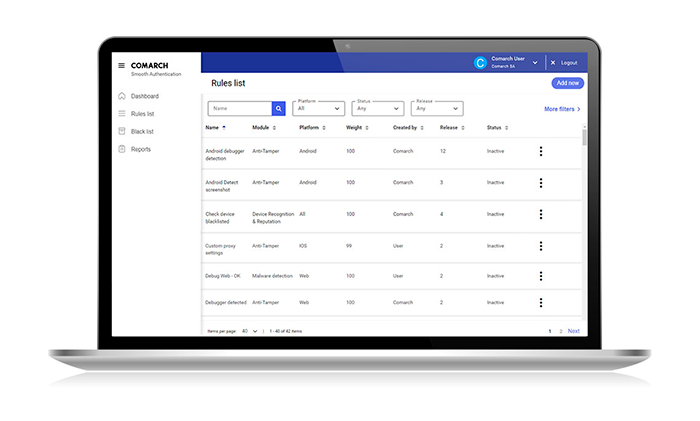
- The possibility to create your own rules and to test them in a dedicated sandbox
- Reduced workload to tackle false positives
- Fewer integration headaches: the possibility to integrate our authentication software with any 2FA solution, including your existing one or our tPro Mobile token – learn more about our comprehensive Comarch Adaptive Authentication Suite
- User-friendly administrator’s console – our risk-based authentication solution is not a black box, you have an insight into the magic happening inside
What’s in Comarch Smooth Authentication for your customers?
- Protection against online frauds during the whole transaction end-to-end, not only log-in process
- Uninterrupted experience with your mobile or web app: Comarch Smooth Authentication software operates in the background without the end user being involved
- No need to download any additional software: our risk based authentication solution is embedded in the app that the customer normally uses
- No friction: the risk based authentication solution limits the need to provide additional verification factors.

Authentication software ready for the future
We won’t leave you alone with your questions. By implementing our effective Smooth Authentication software, we will also provide you with knowledge and experience in cyber security. Our enthusiastic cyber security team constantly monitors the latest fraud scenarios, and our team of ethical hackers tirelessly works on detecting and fighting up-to-date threats in our dedicated Malware LAB. All that so you can benefit from the risk-based authentication software that responds to the newest cyber security challenges.
Red Team / Blue Team-based development
Our product R&D team consists of developers experienced in cyber security, dev-ops and penetration testers. These teams challenge each other in agile sprints, to develop the most advanced fraud detection techniques. Thanks to this approach, our risk-based authentication solution is well-tested against the ingenuity of fraudsters and hackers – in a similar fashion to Red Team / Blue Team-simulated cyberattacks.
Download the Comarch Smooth Authentication leaflet

Download Comarch Smooth Authentication leaflet
Read more about how drive your security by risk-based authentication
Tell us about your business needs. We will find the perfect solution.